Proposal for the monitoring service
Application Status
Status: Completed on 30.08.2021, approved on the 20.01.2021, submitted on the 14.01.2021
Last updated: 14.01.2021
Submited by: Dimitar Ivanov (@dimitar.chain)
Team: Dimitar Ivanov (@dimitar.chain), Ulf Wiger (@uwiger), Dincho Todorov (@dincho.chain)
Approved Budget (in h):
Used Budget (in h):
Planned Delivery:
Specify the funding category
Open Source Development
Application Title
ae_canary, as in “canary in a coal mine”
Applicant
Ulf, Dincho and Dimitar are the maintenance team
Value Application
We will build a service that tracks suspicious accounts. If you consider an
account to be suspicious - you can mark it as so. Then the service will track
any account that the suspicious account sends tokens to. The primary goal of
this is to track the movement of the tokens of the 51% attack.
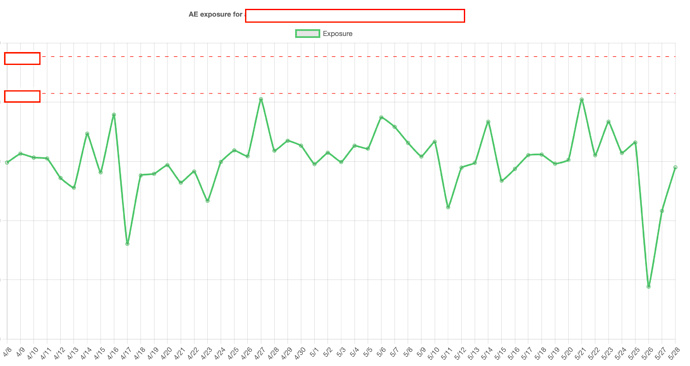
The service will track current exposure of the exchanges: meaning what is the
current amount to be stolen at the moment if there is a 51% attack now. This
is to be used by exchanges for an early alarm. Since it would be based on
heuristics, it could give a false positive.
The service would inform stakeholders when a certain event happens.
Since it will be open source, anyone can deploy it on their server, set their
own accounts to track and own contacts to be informed.
Definition of Terms
We will build as simple a tool as possible, as described above. We aim at
delivering fast so we will cut corners where possible. Let’s call it version
0.1.
Status Quo
No such open source tool is currently available.
Required Work
Ulf and I will build the tool, while Dincho will have our backs.
Estimate
For this v.0.1, we expect a total of 90 man hours.
Known Limitations
The system is expected to work with a limited amount of suspicious accounts and if their count goes in the scope of milions, it will not work; the exposure of accounts alert depends on heuristics which could lead to false positives.
The UI would be as simple as possible. It would be really nice to have proper histograms for example for the exposure but this would certainly require more work.
This system could be extended further in different directions, ex. big fork monitoring across a set of nodes and more.
Outlook
A tool would be given to the community so anyone could set it up for their own needs. Since exchanges are one of the primary users of the network, they are to be its first user but risk management would be important literally for every business on the chain. Basically if you want to be safe, you need all the bells and whistles you can get. This project is one of the bells.
Publishment
It will be open source, sharing the same license as the aeternity node.
Maintenance
This is a one-off, to get it out there as soon as possible. No budgeting had been applied for updating if the APIs it depends on are changed in a backwards incompatible way and etc.
 So short answer would be - if you find the tool useful, yes, do host it. It would not cost you tokens to run it but you’d need to have a MDW running.
So short answer would be - if you find the tool useful, yes, do host it. It would not cost you tokens to run it but you’d need to have a MDW running.